From Scanners to Smart Systems: The Evolution of Vulnerability Management
How AI and machine learning are transforming the four-phase vulnerability lifecycle from a slow, reactive discipline into a continuous, intelligent defense that operates at the speed of modern threats
In the ever-shifting battlefield of cybersecurity, vulnerability management has always been one of the most critical disciplines in a security team’s arsenal. The core objective has never changed: find weaknesses before attackers do, fix them, and confirm they are gone. But the methods, tools, and speed at which this work happens have undergone a seismic transformation. What once took security teams weeks of painstaking manual effort can now be accomplished in hours and, in some cases, autonomously. To appreciate how far we have come, it helps to understand where we started.
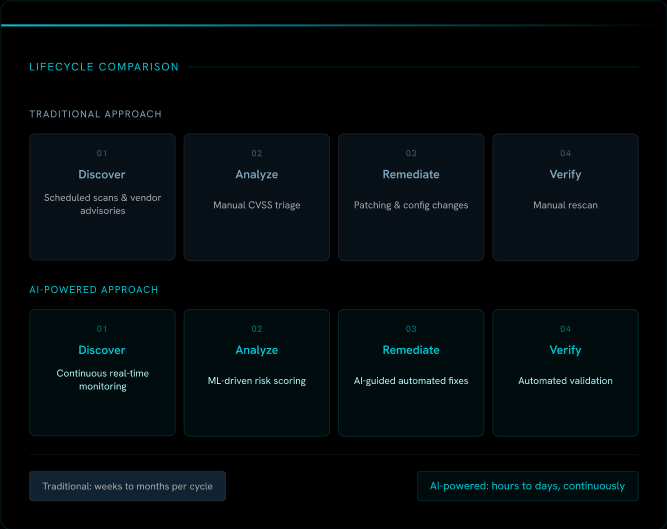
The Traditional Vulnerability Management Lifecycle
For much of the past two decades, vulnerability management followed a structured but sluggish four-phase cycle: discover, analyze, remediate, and verify. Each phase was heavily dependent on human effort, scheduled tooling, and inter-team coordination, a combination that introduced significant delays at every turn.
Thanks for reading! Subscribe for free to receive new posts and support my work.
Discovery: Scanners and Vendor Advisories
The process began with discovery. Security teams deployed network and host-based scanning tools such as Nessus, Qualys, and OpenVAS to sweep IT environments for known vulnerabilities. These scans were typically scheduled weekly, bi-weekly, or even monthly, depending on the organization’s resources and risk appetite. Between scan windows, newly disclosed vulnerabilities went undetected, leaving organizations blind to emerging threats for days or weeks at a time.
Alongside scanners, teams also monitored vendor advisory channels. When Microsoft released its Patch Tuesday updates, or when Cisco, Oracle, or Red Hat published security bulletins, analysts would manually review each advisory, cross-reference affected products in their environment, and flag relevant issues for action. This was time-consuming, reactive work that depended heavily on individual analysts staying on top of a relentless stream of disclosures.
Analysis: Manual Triage and Prioritization
Once vulnerabilities were identified, the next challenge was figuring out which ones actually mattered. Security teams leaned on the Common Vulnerability Scoring System (CVSS) to assess severity, but CVSS scores alone were a blunt instrument. A critical-rated vulnerability on a system with no internet exposure might pose far less risk than a medium-rated flaw on a publicly accessible server handling sensitive data.
This contextual analysis was largely manual. Analysts had to correlate vulnerability data with asset inventories, network topology, and business criticality, often working across disconnected spreadsheets and ticketing systems. The result was a slow, inconsistent prioritization process where the most dangerous vulnerabilities did not always rise to the top fast enough.
Remediation: Patching and Configuration Changes
With a prioritized list in hand, security teams handed off remediation tasks to IT operations. Patches needed to be tested before deployment to avoid breaking production systems. Change management processes required approvals. Maintenance windows had to be scheduled. For large enterprises managing thousands of assets across distributed environments, this coordination overhead was enormous.
The 2017 Equifax breach, one of the most damaging in history, resulted from a vulnerability that had been publicly disclosed and patched 78 days before it was exploited. The patch simply was not applied in time.
Verification: Confirming the Fix
The final phase, verification, was often the most overlooked. After remediation, teams needed to confirm that the fix had actually worked. This typically meant running another manual scan, reviewing results, and closing out tickets. In busy environments, this step was sometimes skipped entirely, leaving teams falsely confident that vulnerabilities had been resolved when they had not.
Taken together, the traditional vulnerability management lifecycle was reactive, labor-intensive, and structurally slow. It was designed for a threat landscape that no longer exists.
How AI Has Transformed Vulnerability Management
The emergence of AI and machine learning has fundamentally reimagined every phase of this process, not by replacing human judgment entirely, but by dramatically augmenting it with speed, scale, and intelligence that no manual process can match.
Smarter, Continuous Discovery
AI-powered platforms have eliminated the concept of scheduled scans. Modern tools continuously monitor environments in real time, detecting new assets as they come online, identifying configuration changes, and flagging vulnerabilities the moment they are disclosed. Integrated threat intelligence feeds allow these platforms to correlate newly published CVEs against an organization’s specific asset inventory automatically, so no analyst needs to read through vendor bulletins line by line. Discovery is now a living, breathing process rather than a periodic snapshot.
Intelligent, Context-Aware Analysis
Where traditional analysis relied on CVSS scores and manual judgment, AI brings a far more sophisticated approach to prioritization. Machine learning models ingest data from multiple sources simultaneously — threat intelligence feeds, active exploit databases, asset criticality ratings, network exposure data, and historical attack patterns — to generate dynamic risk scores that reflect real-world danger rather than theoretical severity. Vulnerabilities being actively exploited in the wild are automatically elevated. Those affecting isolated, low-value assets are deprioritized. The result is a focused, actionable list that directs human attention where it matters most.
Accelerated, Guided Remediation
AI has also transformed how organizations respond to vulnerabilities. Intelligent platforms now generate context-aware remediation recommendations, suggesting the most effective fix for each vulnerability based on the specific environment. In some cases, AI-driven automation handles routine patches entirely autonomously, without requiring human intervention. For more complex or high-risk changes, AI prepares detailed remediation playbooks that reduce the cognitive burden on operations teams and accelerate execution. What once took weeks of back-and-forth coordination can now be resolved in hours.
Automated Verification
Perhaps the most underappreciated AI contribution is in verification. Automated systems now validate remediation outcomes in near real time, continuously re-evaluating the environment after changes are made and confirming that vulnerabilities have been fully resolved. This removes the risk of fixes being assumed rather than confirmed, and it closes the feedback loop far faster than any manual rescan could.
78 Days between patch release and the Equifax breach A defining failure of the traditional vulnerability management model, and a cautionary reminder of what delayed remediation costs in the real world.
A New Standard for Cyber Resilience
The evolution of vulnerability management is ultimately a story about keeping pace with adversaries. Attackers today are fast, automated, and opportunistic. They scan the internet for vulnerable systems within hours of a new CVE being published. The traditional vulnerability management cycle, with its weekly scans and multi-week remediation timelines, was never built to compete with that reality.
AI has closed the gap. By transforming vulnerability management from a periodic, reactive process into a continuous, intelligent defense, organizations can now operate at the speed the modern threat landscape demands. The tools have changed. The timelines have changed. And for security teams willing to embrace this evolution, the outcome is a meaningfully stronger security posture across the board