From Checklists to Continuous Compliance: How AI Is Transforming GRC
AI is turning Governance, Risk, and Compliance from a backward-looking audit exercise into a real-time, intelligence-driven function that keeps pace with the actual threat landscape.

For decades, Governance, Risk, and Compliance — GRC — has been one of the most resource-intensive and least glamorous corners of cybersecurity. While penetration testers and threat hunters operate at the sharp edge of the discipline, GRC teams have largely toiled in spreadsheets, email chains, and audit portals, manually gathering evidence, maintaining risk registers, and preparing for assessments that happen once a year whether the organization is ready or not. AI is now rewriting this reality, turning GRC from a backward-looking compliance exercise into a forward-looking, continuously operating risk intelligence function.
The Traditional GRC Model: Built for a Slower World
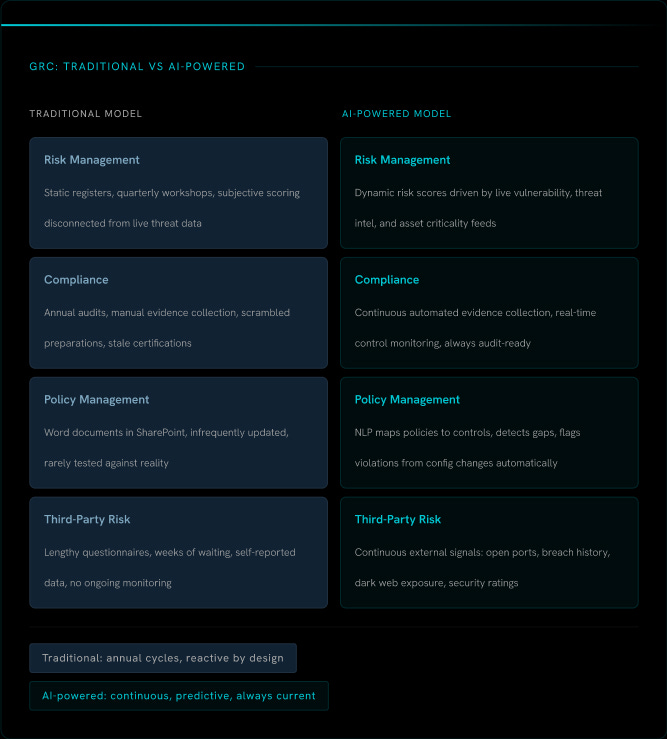
To appreciate the magnitude of this shift, it is worth understanding just how manual and fragmented traditional GRC has always been. The discipline spans four interconnected domains — risk management, compliance, policy management, and third-party risk — and in the traditional model, each one suffered from the same structural flaw: it was designed to produce a point-in-time snapshot rather than continuous situational awareness.
Risk Management: Static Registers and Annual Reviews
In the traditional model, risk management began with the construction of a risk register — a document listing known risks, their likelihood, their potential impact, and the controls in place to mitigate them. These registers were built through workshops and interviews, populated by hand, and reviewed on a quarterly or annual basis. By the time a risk register was finalized and approved, the threat landscape it was designed to reflect had already changed.
The deeper problem was that traditional risk registers were disconnected from real-world threat intelligence. A risk might be rated “medium” based on someone’s subjective judgment in a workshop two quarters ago, with no mechanism to automatically escalate it when a new exploit targeting that exact exposure was published the following week. Risk scores were opinions, not signals.
Compliance Management: The Annual Audit Treadmill
Compliance management in the traditional model was built around a single event: the audit. Whether the framework in question was SOC 2, ISO 27001, PCI DSS, HIPAA, or NIST, the pattern was the same. An assessment date was set, teams scrambled to gather evidence — screenshots, configuration exports, policy documents, access logs — from dozens of systems across the organization, and much of this evidence collection was done manually, with staff chasing down system owners over email and compiling artifacts into shared folders for auditors to review.
This process was exhausting, expensive, and produced a result that was only meaningful for a brief window of time. An organization could achieve SOC 2 Type II certification in January and suffer a significant control failure in February, with no mechanism to detect or report it until the next assessment cycle rolled around.
Policy and Control Management: A Documentation Exercise
Policies and controls were documented in Word files and SharePoint libraries, updated infrequently, and rarely tested against actual operational reality. Control owners were assigned on paper, but whether those controls were being executed consistently in practice was largely a matter of trust and manual spot-checking. Gaps between documented controls and operational reality could persist for months without detection.
Third-Party Risk: Questionnaires and Hope
Third-party risk management was perhaps the weakest link in the traditional GRC model. Organizations sent lengthy security questionnaires to vendors, waited weeks for responses, reviewed answers subjectively, and filed the results away. Whether a vendor’s security posture had deteriorated since they last completed a questionnaire was essentially unknown until the next assessment cycle, or until a breach occurred.
The limitations of traditional GRC were not the result of a lack of effort or expertise. They were structural. The volume of data required to manage risk and compliance accurately simply exceeded what any human team could process manually and continuously. AI removes that constraint entirely.
Continuous Risk Monitoring and Dynamic Scoring
AI-powered GRC platforms have replaced the static risk register with a continuously updated risk intelligence model. Rather than relying on subjective workshop outputs, these platforms ingest data from vulnerability scanners, threat intelligence feeds, endpoint detection systems, cloud configuration tools, and external attack surface monitoring services, synthesizing it all into dynamic risk scores that reflect the current state of the environment.
When a new critical vulnerability is disclosed, the platform automatically assesses whether any assets in scope are affected, correlates that exposure with known exploit activity in the wild, and escalates the associated risk items in real time. Risk scores are no longer opinions formed in a workshop. They are living signals derived from actual data, updated continuously as the environment and the threat landscape evolve.
Automated Evidence Collection and Continuous Compliance
Perhaps the most transformative AI contribution to GRC is in compliance management. AI-powered platforms now integrate directly with cloud environments, identity providers, endpoint management systems, and SaaS applications to collect compliance evidence automatically and continuously. Rather than scrambling to pull screenshots before an audit, organizations maintain a living, always-current evidence repository that maps directly to the controls required by their applicable frameworks.
This shift has profound implications. Instead of achieving compliance once a year and hoping nothing breaks before the next audit, organizations can monitor their compliance posture in real time. Control failures are detected immediately, not discovered by an auditor months later. The gap between documented controls and operational reality collapses because the platform is observing operational reality directly, not relying on self-reported data.
AI-Driven Policy Intelligence
AI is also transforming how organizations manage and apply policies. Natural language processing now enables GRC platforms to map policy requirements automatically to technical controls, identify gaps between policy intent and implemented configurations, and flag when system changes introduce policy violations. Policies are no longer static documents that gather dust between reviews. They become active inputs into a continuous monitoring process that verifies compliance with them in practice, not just on paper.
Intelligent Third-Party Risk Management
The transformation of third-party risk management is particularly striking. AI-powered platforms now assess vendor security posture continuously using external signals — open port scanning, certificate monitoring, dark web exposure data, breach history, and security rating feeds — without relying on self-reported questionnaire responses. Organizations gain a real-time view of how their vendor ecosystem’s risk profile is changing, and can set automated alerts when a key vendor’s security rating drops below an acceptable threshold. The questionnaire does not disappear entirely, but it is no longer the primary signal.
60% Of breaches involve a third party Yet traditional vendor risk management relied almost entirely on self-reported questionnaire data reviewed annually. AI-powered continuous monitoring closes this gap with real-time external signals.
From Reporting to Prediction
Perhaps the most forward-looking capability AI brings to GRC is predictive risk analytics. By analyzing historical risk and control data alongside external threat intelligence, AI models can now identify which controls are most likely to fail, which business units carry the highest concentration of unmitigated risk, and where the next significant exposure is most likely to emerge. GRC leadership can shift from reporting on what has already happened to advising the business on what is likely to happen next — a transformation from a compliance function to a genuine strategic risk intelligence capability.
A New Role for GRC Professionals
It is worth addressing a concern that often arises in this conversation: whether AI is replacing GRC professionals. The answer is clearly no, but the role is evolving significantly. The GRC professional of the near future will spend far less time on manual evidence collection, questionnaire management, and spreadsheet maintenance, and far more time on risk interpretation, control strategy, and business-facing risk communication. AI handles the data gathering and pattern recognition. Human judgment remains essential for deciding what the data means and what to do about it.
The Bottom Line
Traditional GRC was built for an era when annual audits and quarterly risk reviews were considered sufficient. In a threat landscape where material changes to an organization’s risk posture can occur overnight, that cadence is no longer defensible. AI transforms GRC from a compliance calendar into a continuous risk intelligence operation — one that monitors the environment in real time, detects control failures the moment they occur, and gives leadership the forward-looking insight they need to make informed decisions. The checklist is not gone. But for the first time, the checklist actually keeps up with reality.